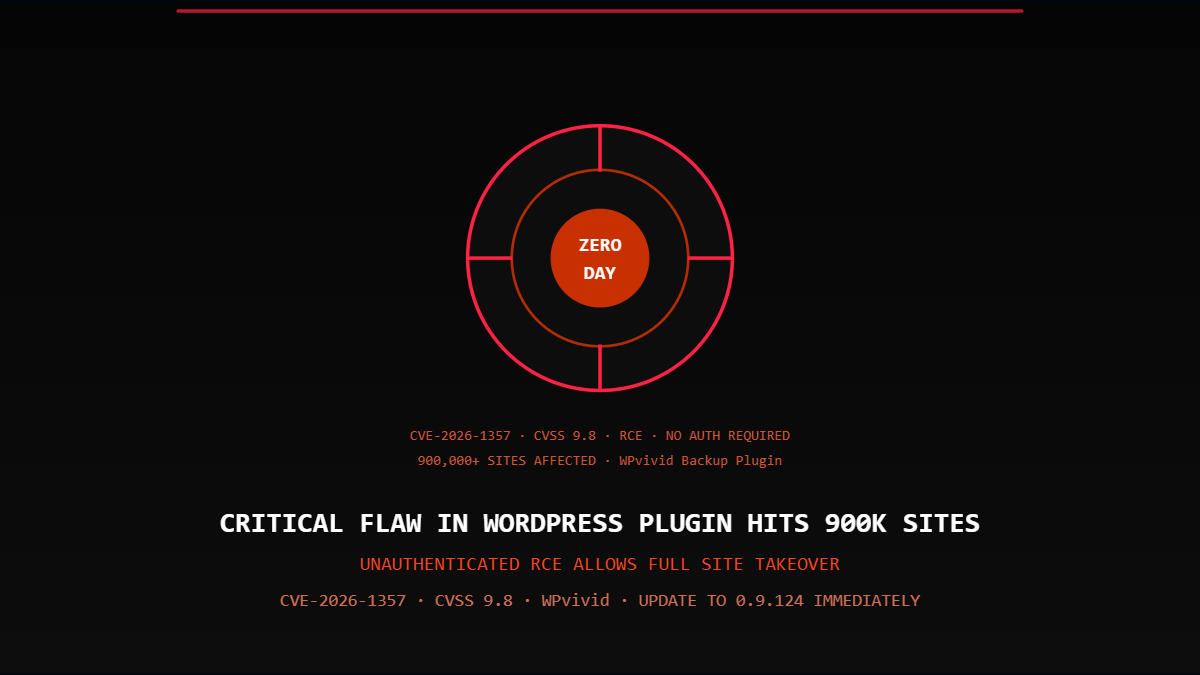
A critical security vulnerability has been discovered in the WPvivid Backup & Migration plugin for WordPress — a widely used tool installed on more than 900,000 websites worldwide. The flaw, tracked as CVE-2026-1357 with a CVSS severity score of 9.8 out of 10, allows unauthenticated attackers to upload arbitrary files to the server and achieve remote code execution (RCE), potentially resulting in a complete website takeover.
How the Vulnerability Works
Researchers at WordPress security firm Defiant discovered that the plugin suffers from improper error handling in its RSA decryption process, combined with a lack of path sanitization. This combination allows threat actors to upload malicious files to the server without needing any authentication credentials. The bug affects all plugin versions up to and including 0.9.123. A patch was released in version 0.9.124.
However, there is an important caveat: only sites that have the “receive backup from another site” option enabled are critically exposed. This feature is not turned on by default, but it is commonly activated by site administrators who use the plugin for migrations and backup transfers between hosting environments. Additionally, the exploitation window is limited to 24 hours, as the generated key required by sending sites expires within that timeframe.
What Attackers Can Do With It
Successful exploitation grants attackers full administrative control over the affected WordPress site. From there, they can install backdoors for persistent access, exfiltrate user data and credentials, inject malicious scripts to distribute malware to visitors, deface the site, or use the compromised server as a launchpad for attacks on other systems. Compromised sites are commonly leveraged for SEO spam, phishing pages, or as part of botnet infrastructure.
What You Should Do Right Now
If you or your organization runs a WordPress site with the WPvivid Backup & Migration plugin installed, update to version 0.9.124 immediately. If an immediate update is not possible, disable the “receive backup from another site” feature until the patch can be applied. This vulnerability is a reminder that plugin hygiene — keeping all components updated, removing unused plugins, and auditing third-party extensions regularly — is not optional. In a WordPress ecosystem where millions of sites share the same plugins, a single unpatched vulnerability can become a mass exploitation event within hours.